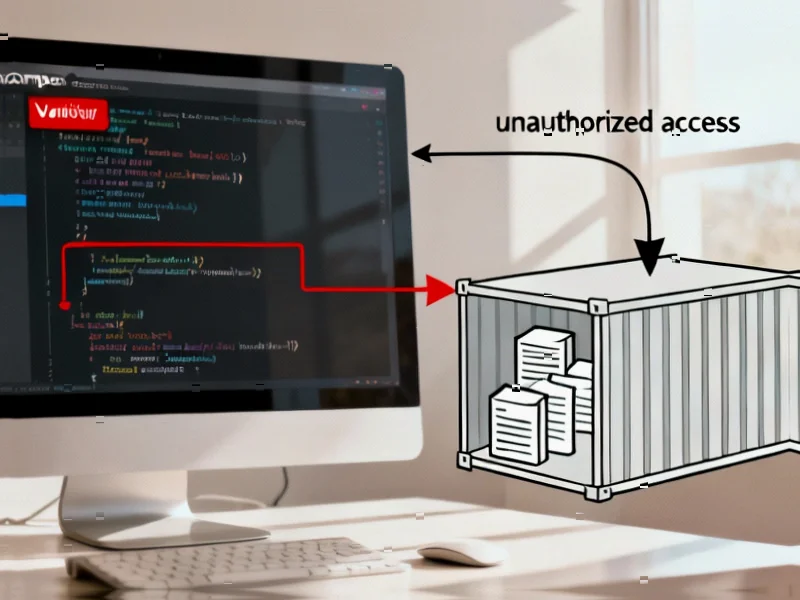
WordPress Security Paradox: Anti-Malware Plugin Creates Backdoor Risk
A security plugin designed to protect WordPress sites has become the vulnerability itself. The Anti-Malware Security and Brute-Force Firewall plugin contains a critical flaw exposing site configuration files to attackers. Here’s what website owners need to know.